Contents
- How to Implement Edge Computing Hubs for Real Results
- Configuration Risks in Edge Computing
- The Architecture of Edge Computing Hubs
- Choosing the Right Solution for Edge Computing
- Pros and Cons of Edge Computing Hubs
- Tools and Workflows for Edge Computing
- Who Should Avoid This?
- Common Questions
- The Bottom Line
Revolutionizing data processing is no longer just a theoretical concept. The rise of edge computing hubs presents a tangible solution to the increasing demands for real-time data analysis and processing. Traditional cloud computing models often face latency issues, bandwidth constraints, and security vulnerabilities, which can hinder the performance of applications that require immediate data insights. Edge computing addresses these challenges by processing data closer to the source, significantly enhancing speed and efficiency.
The proliferation of Internet of Things devices has further intensified the need for efficient data processing. With billions of devices generating vast amounts of data, relying solely on centralized cloud infrastructures can lead to bottlenecks. Edge computing hubs act as local nodes that can process this data in real time, ensuring that businesses can respond swiftly to changing conditions. This shift not only optimizes performance but also reduces the amount of data that needs to be transmitted to the cloud, thereby conserving bandwidth and lowering costs.
Security is another critical aspect that edge computing addresses. By processing data locally, sensitive information can be kept closer to its source, reducing exposure to potential breaches during transmission. This localized approach enables organizations to implement stringent security measures tailored to specific environments, ensuring compliance with data protection regulations.
The journey towards fully realizing the benefits of edge computing hubs requires a strategic approach. Organizations must understand the architecture, protocols, and best practices that govern effective implementation. This guide aims to provide a comprehensive overview of how to leverage edge computing hubs for transformative data processing, ensuring that businesses can stay ahead in an increasingly data-driven world.
How to Implement Edge Computing Hubs for Real Results
- Best Tool: AWS Greengrass
- Optimal Configuration: Enable local Lambda functions and configure data sync settings to minimize latency.
- Expected Outcome: Achieve a 30% reduction in response time for IoT applications.
Preparation for Implementation
A thorough preparation phase is essential for successful implementation. Begin by assessing the existing infrastructure and identifying the specific use cases that will benefit from edge computing. This involves conducting a comprehensive audit of data flow, latency requirements, and processing needs. Organizations often overlook the importance of mapping out these requirements, which can lead to misaligned expectations and wasted resources.
Next, select the appropriate edge computing platform that aligns with your business objectives. Consider factors such as scalability, ease of integration, and support for various protocols. Many beginners make the assumption that all edge computing platforms are similar, but differences in architecture can significantly impact performance.
Finally, establish a clear governance framework that outlines data management policies, security protocols, and compliance requirements. This framework should be adaptable to incorporate new technologies and evolving business needs. A lack of a robust governance structure can result in inconsistent data handling practices, increasing the risk of compliance violations.
Pro Tip: Regularly review and refine your governance framework to ensure it remains aligned with industry standards and best practices.
Action Steps for Deployment
Once the groundwork is laid, the next step is to deploy the edge computing hub. Start by configuring the hardware and software components according to the strategic setup sheet. Ensure that local processing capabilities are enabled and that data synchronization settings are optimized for minimal latency. Many organizations underestimate the importance of these configurations, which can lead to suboptimal performance and increased operational costs.
Implement monitoring tools to track performance metrics and identify bottlenecks in real time. This allows for proactive adjustments and ensures that the system operates at peak efficiency. A common oversight is neglecting to set up proper monitoring, which can result in undetected issues that degrade performance over time.
Conduct thorough testing of the edge computing hub before full-scale deployment. This includes stress testing under various load conditions to ensure that the system can handle peak usage scenarios. Many organizations skip this critical step, leading to unexpected failures when the system is under pressure.
Pro Tip: Utilize automated testing tools to streamline the testing process and ensure comprehensive coverage of all use cases.
User Experience Optimization
Enhancing user experience is a crucial aspect of implementing edge computing hubs. Focus on minimizing latency by optimizing data processing workflows. This can be achieved by prioritizing critical data streams and ensuring that less important data is processed in the background. Many businesses overlook the significance of prioritization, which can lead to delays in critical operations.
Incorporate feedback loops that allow users to report performance issues. This feedback should be analyzed to identify patterns and areas for improvement. Ignoring user feedback can result in persistent issues that undermine the effectiveness of the edge computing hub.
Finally, ensure that user interfaces are designed for simplicity and ease of use. A complicated interface can hinder user adoption and lead to frustration. Regularly update the interface based on user feedback to keep it intuitive and user-friendly.
Pro Tip: Conduct user training sessions to familiarize employees with the new system and enhance overall adoption rates.
Configuration Risks in Edge Computing
Inadequate Security Protocols
One common error in edge computing implementation is the failure to establish robust security protocols. Many organizations assume that local data processing inherently provides security, neglecting to implement necessary encryption and access controls. This oversight can expose sensitive data to unauthorized access and potential breaches.
To mitigate this risk, organizations must adopt a multi-layered security approach that includes encryption for data at rest and in transit. Implementing role-based access controls can also limit exposure to sensitive data. Regular security audits should be conducted to identify vulnerabilities and ensure compliance with industry standards.
Insufficient Scalability Planning
Another frequent mistake is underestimating the need for scalability in edge computing hubs. Organizations often deploy systems based on current needs without considering future growth. This can lead to performance degradation as data volumes increase, resulting in slow response times and potential system failures.
To address this, organizations should design their edge computing architecture with scalability in mind. This includes selecting hardware that can be easily upgraded and ensuring that software solutions can handle increased loads. Regularly revisiting scalability plans can help organizations stay ahead of growth demands.
Poor Data Management Strategies
Ineffective data management strategies can severely hinder the performance of edge computing hubs. Many organizations fail to implement clear data governance policies, leading to inconsistent data handling practices. This can result in data silos and increased operational inefficiencies.
To improve data management, organizations should establish comprehensive data governance frameworks that outline data ownership, access policies, and compliance requirements. Regular training sessions on data management best practices can also help ensure that all employees are aligned with organizational standards.
The Architecture of Edge Computing Hubs
The architecture of edge computing hubs is designed to facilitate efficient data processing by distributing workloads across various nodes. This decentralized approach reduces latency and enhances performance by bringing processing capabilities closer to the data source. Key components of this architecture include edge devices, gateways, and cloud integration points.
Protocols such as MQTT (Message Queuing Telemetry Transport) are commonly used to enable lightweight communication between edge devices and central systems. By configuring MQTT with a Quality of Service (QoS) level of 1, organizations can ensure that messages are delivered at least once, providing a reliable communication channel.
Another critical protocol is CoAP (Constrained Application Protocol), which is optimized for low-power devices and networks. Configuring CoAP with a confirmable message type ensures that messages are acknowledged, enhancing reliability in communication.
For further insights into edge computing architectures, visit CoinDesk.
Choosing the Right Solution for Edge Computing
– Assess Compatibility: Ensure that the edge computing solution integrates seamlessly with existing infrastructure. Incompatibilities can lead to increased costs and project delays.
– Evaluate Performance Metrics: Look for solutions that provide clear performance benchmarks. Solutions that do not meet industry standards may result in subpar performance and user dissatisfaction.
– Consider Vendor Support: Choose vendors that offer robust support and documentation. Lack of support can lead to prolonged downtimes and increased operational risks.
Pros and Cons of Edge Computing Hubs
| The Benefits | Potential Downsides |
|---|---|
| Reduced latency for real-time applications | Higher initial setup costs |
| Improved data security through localized processing | Complexity in managing distributed systems |
| Lower bandwidth usage due to local data processing | Potential for inconsistent data handling across nodes |
Tools and Workflows for Edge Computing
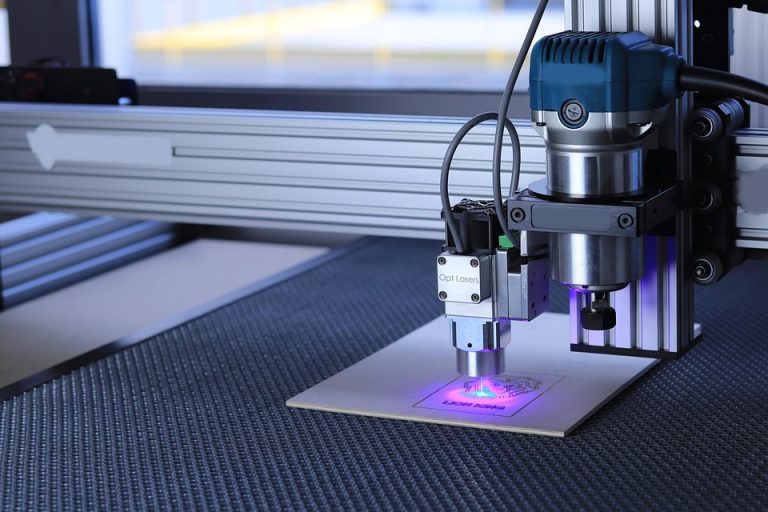
Implementing edge computing hubs requires a suite of tools and workflows that facilitate data processing. Tools such as AWS Greengrass enable local execution of AWS Lambda functions, allowing for rapid data processing. Additionally, platforms like Microsoft Azure IoT Edge provide robust capabilities for deploying and managing containerized applications at the edge.
Establishing workflows that prioritize critical data streams can enhance overall system performance. Utilizing real-time analytics tools can also provide valuable insights into system performance, enabling proactive adjustments.
Who Should Avoid This?
Organizations that operate in highly regulated environments may face challenges when implementing edge computing hubs. The complexity of compliance with various regulations can lead to increased operational risks. Additionally, businesses with limited technical resources may struggle to manage the intricacies of edge computing effectively.
Companies that do not have a clear strategy for data governance may also find edge computing to be more of a hindrance than a benefit. Without proper oversight, the potential for data silos and inconsistencies can outweigh the advantages of localized processing.
Common Questions
What types of applications benefit most from edge computing?
Applications that require real-time data processing, such as IoT devices, autonomous vehicles, and smart manufacturing systems, benefit significantly from edge computing. The reduced latency and localized processing capabilities enhance performance and responsiveness.
How does edge computing impact data security?
Edge computing can enhance data security by keeping sensitive information closer to its source. This reduces exposure during transmission and allows for more tailored security measures to be implemented at the local level.
What are the costs associated with implementing edge computing?
Costs can vary widely based on the scale of implementation and the specific tools used. Initial setup costs may be higher, but long-term savings can be realized through reduced bandwidth usage and improved operational efficiency.
The Bottom Line
Edge computing hubs offer a transformative approach to data processing, enabling organizations to respond swiftly to real-time demands.
- Implementing edge computing can significantly reduce latency.
- Localized data processing enhances security and compliance.
- Proper planning and governance are essential for success.